Every large organization uses some form of physical access control today. Access badges, fobs, PIN codes, biometrics, mobile credentials or a combination of each are traditionally used to control physical access to the organization’s facilities. The end goal is protecting critical assets, which includes physical goods (e.g., expensive equipment), Intellectual Property (e.g., company data on computers) or people (e.g., hazardous environments).
The larger the organization, and the more an organization scales, the harder it becomes to keep physical access control in lockstep with the business. New employees start on a daily basis, people change roles, people travel or move to another location, contractors come and go, visitors are welcomed in various locations, etc. Keeping up with this volume of changes becomes mission impossible.
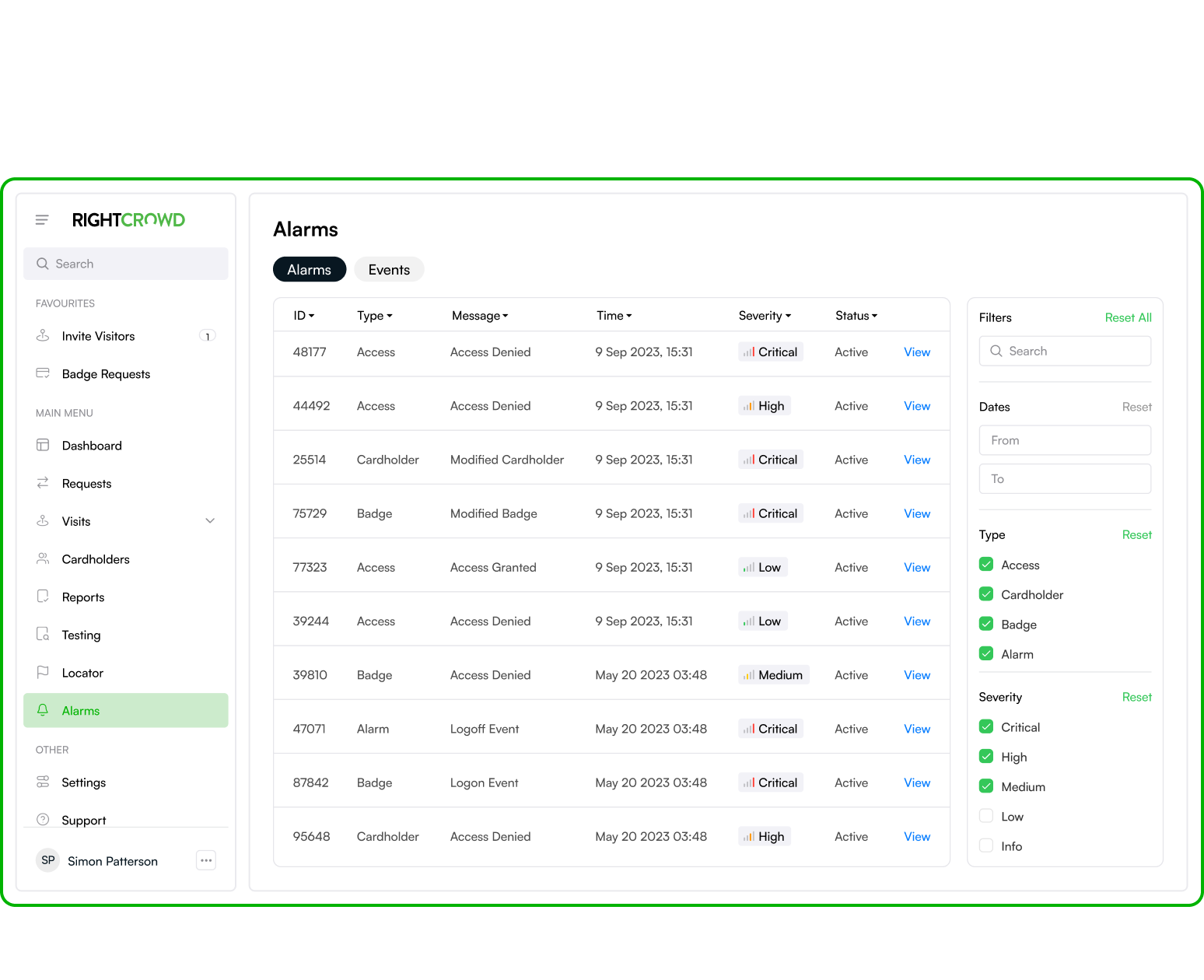
That is where Physical Identity and Access Management (PIAM) comes to the rescue. Think of putting an intelligent automation and policy layer on top of your existing Physical Access Control System (PACS). Your PACS continues to take care of opening doors, but the PIAM layer on top of it takes care of managing access in a smart and automated way.
So, what value does PIAM add to your existing PACS? It adds automation and enables a dynamic way of managing access.
Automating Physical Access Processes
Here are just a few examples of what a PIAM solution can do:
- Automatically add a new card holder record in your PACS and initiate a badge request when a new employee starts.
- Automatically change access levels when an employee moves to a different location.
- Comes with a self-service portal that allows employees to request additional access.
- Provides a kiosk application that issues temporary badges to employees who forgot their badge (and disables their regular badge until the temporary badge is returned).
A mature PIAM solution doesn’t only handle employees. It also automates visitor registration and contractor on-boarding processes, including additional requirements such as the completion of NDAs, external watchlists or safety videos. In other words, a PIAM solution takes away all manual, error-prone work, without taking away control. As part of such automated workflows, you can still decide which physical access changes require a human validation before being applied.
Attribute-Based Physical Access Control
Automation is one clear benefit of PIAM. But as important is PIAM’s ability to enable what is called attribute-based physical access control (ABAC). If you’re not familiar with the term, it has been borrowed from the digital, logical access control space. With ABAC, instead of statically defining someone’s access or setting it based on a person’s role, you define policies that set and revoke the access of people in a dynamic way based on attributes.
Let’s illustrate with a simple example. In a traditional PACS you statically define that John and Mary have access to the Data Center. If John were to move to a different role, you would be dependent on someone informing you to revoke John’s access to the Data Center. When using attribute-based access control, you don’t set access for individuals, but instead you set policies that determine which access a person should have. In this example, you could have a policy that says, Access to the Data Center is given to persons that are part of the IT department, have an active employment status, are located in the HQ facilities and have successfully passed the ISO27001 training’. If John were to move to a different role, the PIAM system would automatically pick that up from you HR system, and the above policy would automatically remove John’s access to the Data Center.
Implementing a PIAM Solution
Historically, PIAM deployments have been challenging due to their complexity, timeline for completion and resource coordination requirements. This was mainly a result of the software being immature, often requiring custom development to meet the specific business process, security and safety policies of the customer. With modern PIAM solutions, customers have options. A ”Best-Practice based” solution incorporates common functionality used in most PIAM deployments and typically takes weeks to a few months to implement. Or ”Customer-Specific” deployments that address and align the unique processes and policies of the business with the PIAM. These typically take longer and are based on milestones with specific benefits and value at each stage.
To find out more about RightCrowd PIAM solutions contact us.