According to the first-ever World Security Report, large, global companies lost a combined $1 trillion in revenue in 2022 due to physical security incidents. The report also found that companies anticipate a surge in threats and hazards like social unrest, climate change, fraud and theft. As a result, physical security budgets are predicted to increase significantly to keep people, property and assets safe.
Banks and financial institutions are increasingly expressing concerns over the escalating risks posed by insider threats, both in terms of physical security and cybersecurity – and with good reason. A recent report by Searchlight Cyber, titled “Dark Web Threats Against The Banking Sector,” highlights instances where bank employees openly discuss their ability to compromise security within their own premises.
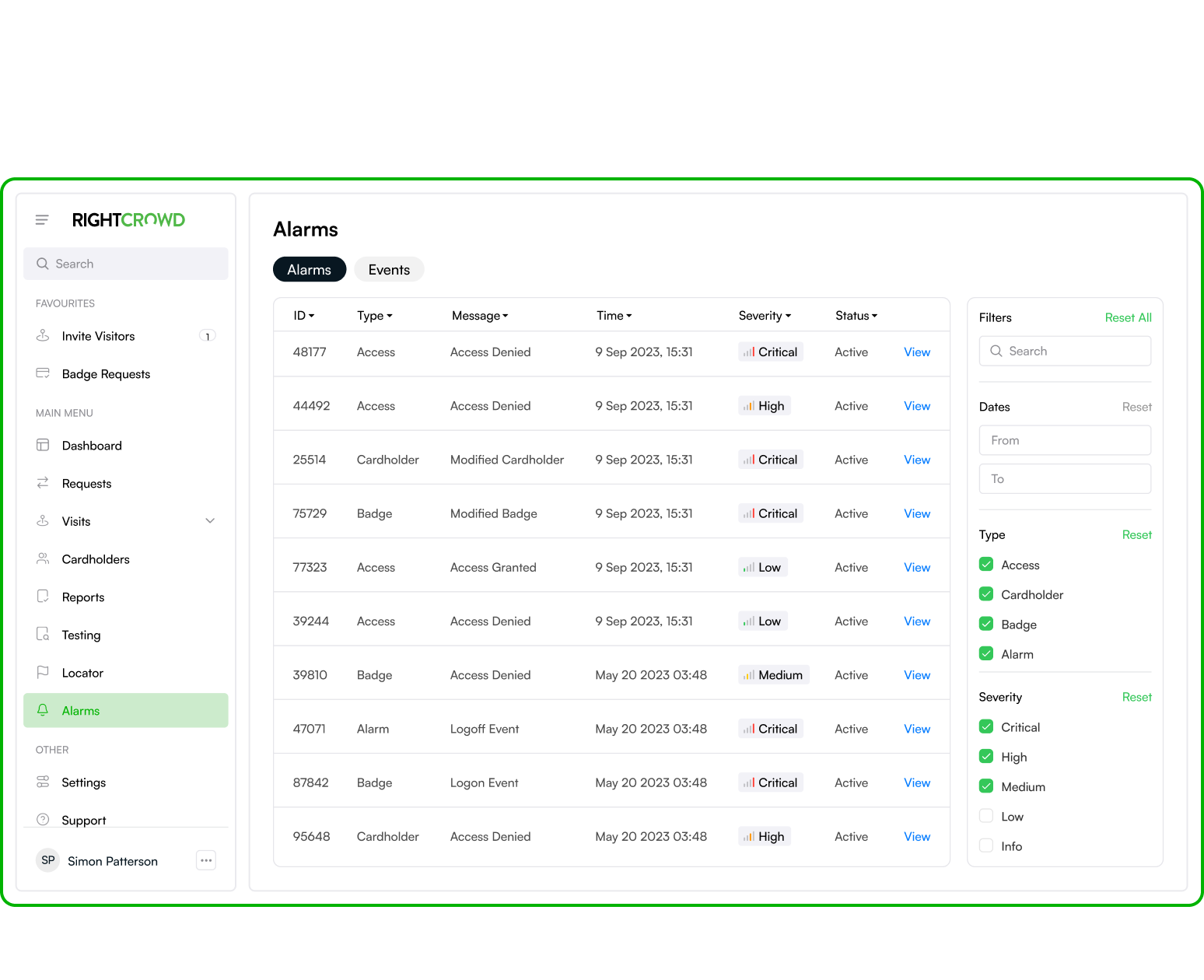
This underscores the critical importance of robust physical access controls, identity verification, and real-time alerting functions – all achievable through the implementation of automated Physical Identity Access Management (PIAM) and Threat Intelligence Solutions. This is why multiple “Tier One” banks trust RightCrowd as their PIAM system.
To grasp the value that PIAM and Threat Intelligence solutions bring to a company, it’s helpful to contrast them with traditional access management methods and the challenges associated with legacy access control systems and manual processes. In the absence of PIAM, access management typically relies on a process involving an organization’s security department, Human Resources (HR) department and department managers. In other words, manual processes ripe for human error, delays and therefore increased risk. These departments often work in isolation when determining appropriate access privileges for staff and visitors, issuing credentials, and provisioning access on a case-by-case basis.
Cutting-edge PIAM solutions transform access management by harnessing data-driven automation. These advanced systems aggregate and analyze a vast array of data, including identities, credentials, permissions, and information from various business systems such as HR software and Learning Management software to make your Physical Access Control System (PACS) “smart.” This comprehensive data intelligence provides organizations with enterprise-wide visibility throughout the entire lifecycle of identities. By centralizing identity management on a single platform, PIAM automates the access provisioning process, granting access permissions based on roles and approval rules. This automation minimizes the risk of errors, unintended privileges and streamlines onboarding and offboarding processes.
Next-generation PIAM also automates the detection and identification of insider threats. Insider threats pose challenges in detection due to their deceptive nature. Modern Threat Intelligence software utilizes machine learning algorithms to uncover access anomalies and suspicious activities by analyzing data from various access control parameters such as timestamps, locations, credential usage and transaction patterns. Moreover, administrators can exert greater control over the access they provide, mitigating the impact of insider threats.
RightCrowd software, which is an advanced PIAM solution, offers capabilities that will transform your organization’s safety protocols to reduce risk, including:
- Fully automated physical access management requests and approvals
- Fully automated identity lifecycle from onboarding to offboarding
- Real-time monitoring and proactive alerts
- Compliance assurance
- Limiting lateral movement within a facility
- Establishing identity assurance through a robust multi-factor authentication architecture
And much more…
In this manner, PIAM solutions present a comprehensive approach to bolstering bank and finance security, integrating physical and digital safeguards to ensure a robust defense against both cyber and physical threats.